Al-Ahliyya Amman University
Program Description
Master in Cyber Security
Master
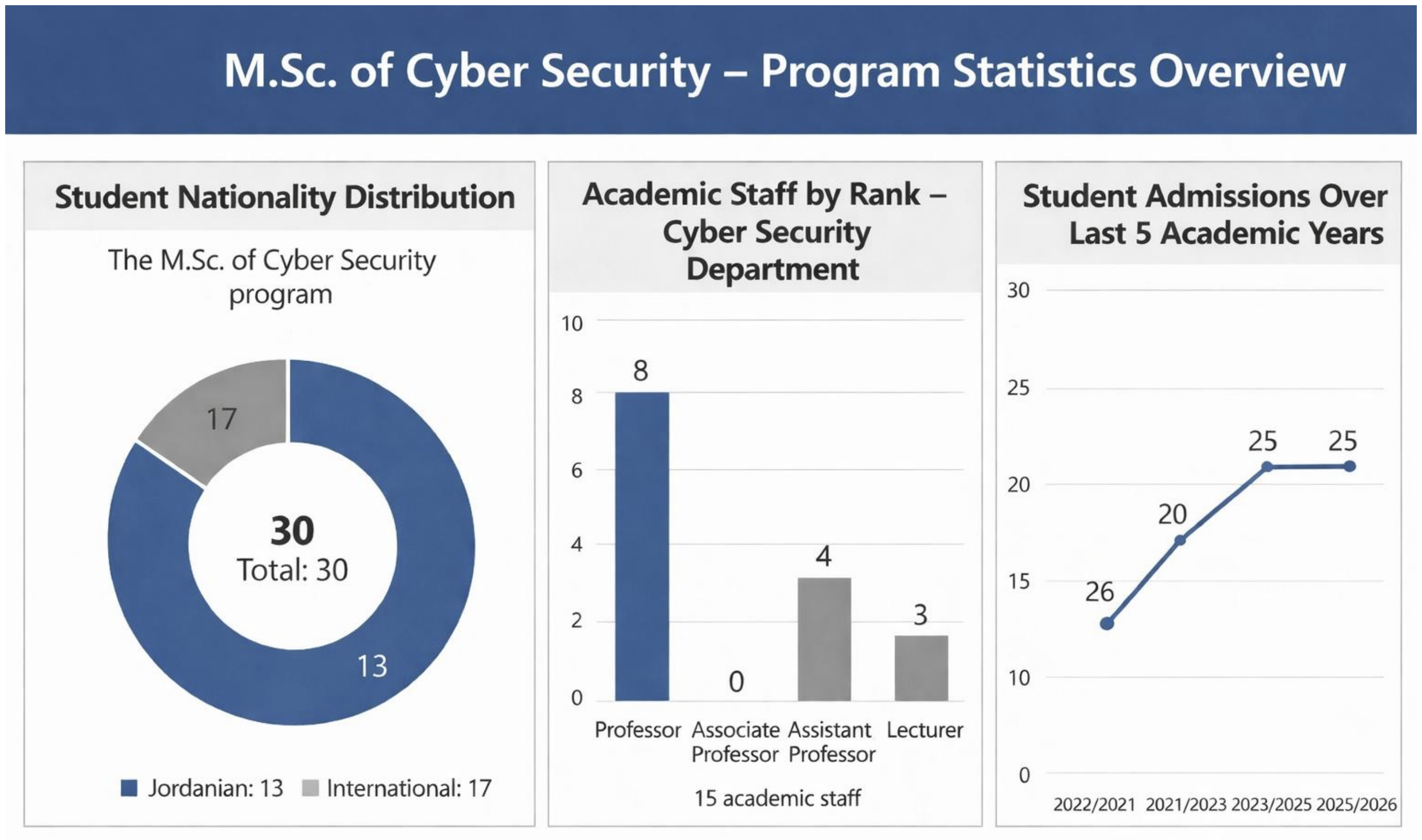
The Master’s in Cybersecurity program was established in 2021 with the goal of providing local and regional labor markets with graduates who possess advanced knowledge and practical experience in information security, risk management, and cyber defense. The program aligns with the vision of the College of Information Technology, which seeks to offer high-quality education in an innovative learning environment that keeps up with the latest developments in cybersecurity and digital
technologies. The program aims to equip graduates with technical knowledge and leadership skills that meet labor market needs and keep pace with ongoing changes in this field.
The program offers a comprehensive curriculum that combines theoretical foundations with practical applications, based on the latest technologies and methodologies used to protect information systems and digital infrastructures. Students gain in-depth skills in analyzing, assessing, and mitigating security threats across various computing environments.
The Master in Cybersecurity program focuses on advanced topics such as cryptography and secure protocols, network and system security, ethical hacking and penetration testing, digital forensics and incident response, security governance and risk management, privacy and data protection, and secure software engineering practices. Additionally, the program includes specialized research, projects, and case studies that prepare students to contribute to both academia and industry.
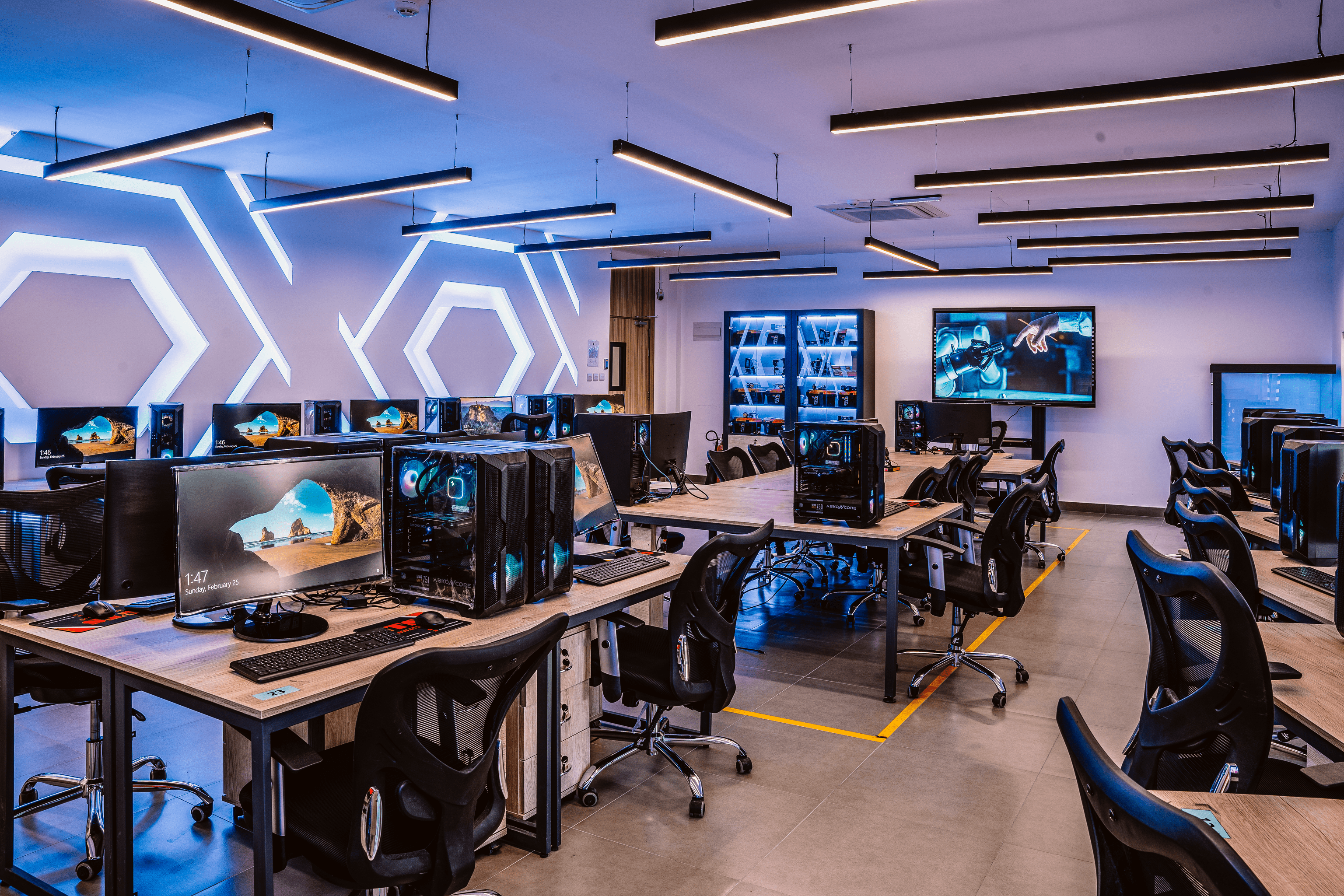
A key component of the program is the Master’s Thesis, where students apply research methods and security solutions to real-world problems under the supervision of faculty. Practical labs, simulations, and collaborative activities further enhance students’ readiness to protect and defend information assets in professional environments.
Upon graduation, students are equipped not only with advanced theoretical understanding but also with hands-on expertise and ethical competencies that support strategic decision-making in cybersecurity. Graduates are prepared to take on leadership roles in government agencies, private sector enterprises, critical infrastructure organizations, and research institutions, while contributing to innovation and sustainable development in the digital age.
Admission Requirements
Admission to the Master’s in Cyber Security program requires that the applicant holds bachelor’s in cyber security or any related IT field .
Job Opportunities
- Cybersecurity Analyst
o Monitors threats, responds to incidents, and protects systems and data. - Network Security Engineer
o Design, implement, and maintain security solutions to protect an organization’s network infrastructure from cyber threats. This includes managing firewalls, intrusion detection systems, and VPNs. - Information Security Manager
o Oversees security policies, strategies, and cybersecurity operations within an organization. - Incident Response Analyst
o Investigates cyber incidents, supports recovery, and helps prevent future attacks. - Penetration Tester (Ethical Hacker)
o Identifies vulnerabilities by conducting authorized security tests on systems and applications. - Chief Information Security Officer (CISO)
o Leads the organization’s overall cybersecurity strategy and governance. - Software/Application Security Engineer
o Secures software and applications by identifying and reducing vulnerabilities during development and deployment. - Cloud and Data Security Specialist
o Protects cloud environments and sensitive data through secure architectures, encryption, and access controls. - Cybersecurity Consultant
o Provides expert advice on risk management, security improvement, and compliance.
Program Educational Objectives (PEO's):
-
PEO-1: Professional Success: Graduates will successfully practice in cybersecurity-related professions by applying advanced theoretical and practical competencies to analyze, design, implement, and evaluate secure solutions for complex computing environments.
-
PEO-2: Continuous Professional Development: Graduates will pursue continuous professional development through lifelong learning, specialized training, professional certifications, and adaptation to emerging cybersecurity trends, technologies, and threats.
-
PEO3: Research and Innovation: Graduates will contribute to research and innovation in cybersecurity by investigating complex problems and developing advanced, innovative, and effective solutions that address evolving industry and societal needs.
-
PEO-4: Communication, Leadership, and Ethical Responsibility: Graduates will communicate effectively, work collaboratively, lead technical initiatives, and uphold ethical, legal, and professional standards in cybersecurity practice.
|
PEO |
Key Points in the Mission |
Mapping between Mission and PEO |
|
PEO-1: Professional Success |
Prepares graduates with advanced |
The mission directly supports professional |
|
PEO-2: Continuous Professional Development |
To provide research-informed and practice-oriented graduate education” and to prepare graduates for lifelong learning and adaptation to emerging technologies and professional challenges. |
The mission aligns with continuous professional development by promoting advanced learning, research capability, and sustained engagement with emerging technologies and scientific advancement in the field. |
|
PEO-3: Innovative Contributions |
Fosters excellence, innovation, critical inquiry and contributes to … sustainable community development. |
The mission supports research and innovation by encouraging graduates to apply critical thinking and advanced knowledge to investigate cybersecurity problems and develop innovative solutions that address industry and societal needs |
|
PEO-4: Effective Communication and Ethical Leadership |
Equipping students with leadership skills and technical knowledge that meet the needs of the labor market. |
The mission aligns with this PEO through its emphasis on professional responsibility, leadership, and graduate preparedness, supporting effective communication, collaboration, and ethical conduct in complex professional contexts. |
Students Learning Outcomes (SO's):
- SO1. Demonstrate comprehensive and critical knowledge of cybersecurity principles, technologies, frameworks, and emerging trends.
- SO2. Analyze and evaluate cybersecurity risks, threats, and vulnerabilities, and design, implement, and validate secure systems, networks, and applications that satisfy organizational, regulatory, and ethical requirements.
- SO3. Conduct independent research or applied cybersecurity projects, communicate effectively, work collaboratively, demonstrate ethical and professional responsibility, and engage in continuous learning and professional development.
- SO4. Apply advanced cryptographic, authentication, digital forensics, and incident response techniques to protect digital assets and investigate and mitigate cybersecurity breaches.
- SO5. Demonstrate advanced knowledge of cybersecurity governance, risk management frameworks, legal requirements, standards, and ethical practices, and their alignment with organizational and business objectives.
- SO6. Employ artificial intelligence, automation, and machine learning techniques for threat detection, analysis, and proactive cyber defense.
- SO7. Demonstrate leadership and effective decision-making in managing complex cybersecurity operations and multidisciplinary teams.
Program Learning Outcomes
- PLO1 : Demonstrate comprehensive and critical knowledge of cybersecurity principles, technologies,
frameworks, and emerging trends. (Knowledge) - PLO2: Analyze and evaluate security risks, threats, and vulnerabilities using scientific, analytical, and
technical approaches. (Skills) - PLO3: Design, implement, and validate secure systems, networks, and applications that meet
organizational, regulatory, and ethical requirements. (Skills) - PLO4: Conduct independent research or applied projects that contribute to the advancement of
cybersecurity knowledge or practice. (Competence) - PLO5: Communicate effectively, work collaboratively, and demonstrate ethical and professional
responsibility in diverse cybersecurity contexts. (Competence) - PLO6: Engage in continuous learning and professional development to adapt to evolving
cybersecurity challenges and technologies. (Competence) - PLO7: Apply advanced cryptographic and authentication techniques to ensure data confidentiality,
integrity, and availability. (Skills) - PLO8: Utilize digital forensics tools and incident response techniques to investigate and mitigate
cybersecurity breaches. (Skills) - PLO 9: Integrate risk management frameworks and governance models to align cybersecurity
strategies with business objectives. (Knowledge) - PLO 10: Evaluate and ensure compliance with international and national cybersecurity laws,
standards, and ethical practices. (Knowledge) - PLO11: Employ artificial intelligence, automation, and machine learning for threat detection and
proactive cyber defense. (Skills) - PLO12: Demonstrate leadership and decision-making abilities in managing complex cybersecurity
operations and multidisciplinary teams. (Competence)
Master in Cyber Security
Number Of Credit Hours
33
Faculty of Information Technology
Thesis Track
Comprehensive Track